Ethereum’s Next Big Step towards Scaling: Danksharding
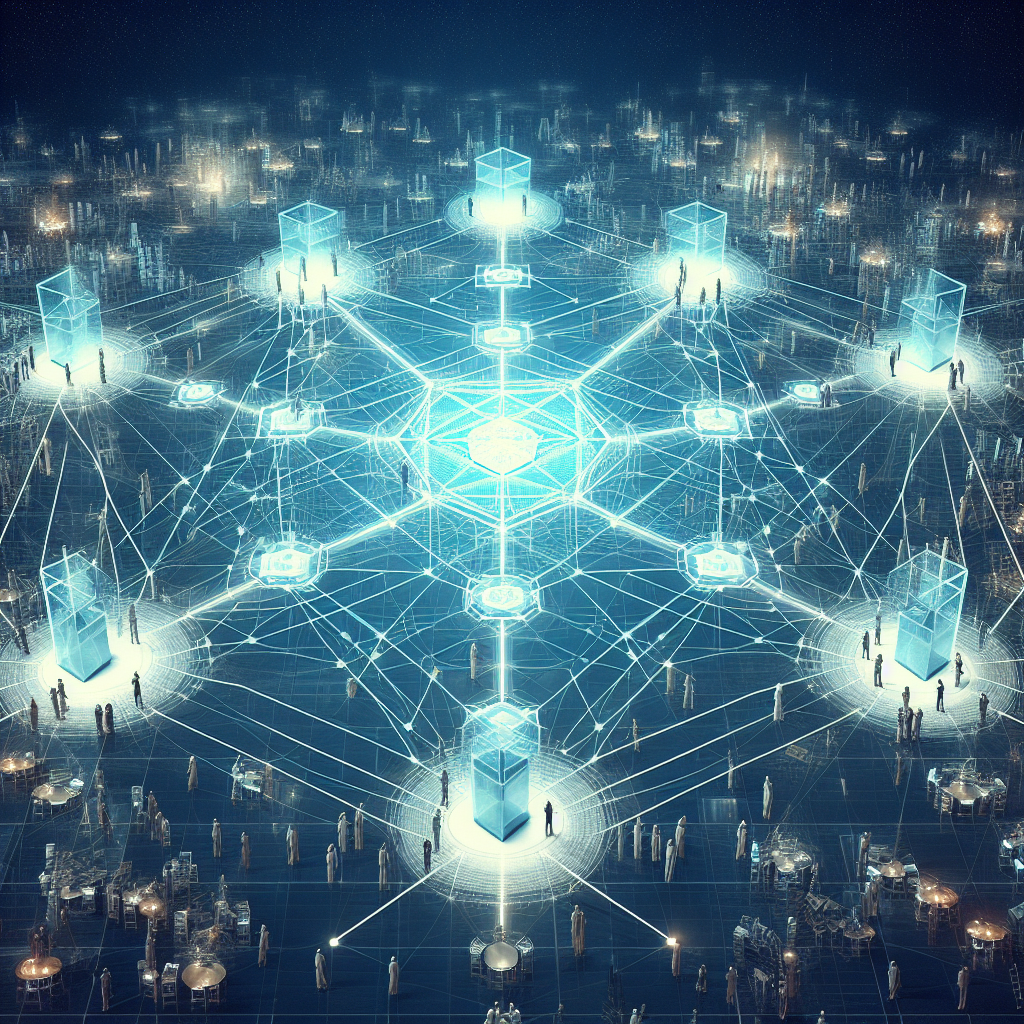
Ethereum, a leading decentralized blockchain platform, is constantly evolving to meet the growing demands of its users. One of the key challenges Ethereum faces is scalability, the ability to handle a large volume of transactions efficiently. Danksharding, a novel sharding solution, has emerged as a promising approach to address this challenge. Traditional Sharding: A Brief Overview Sharding is a technique for dividing a blockchain into smaller, more manageable segments called shards. This allows the network to process transactions in parallel, improving overall throughput and reducing congestion. In traditional sharding, each shard is responsible for maintaining a subset of the network’s…